Introduction:
Is America a Democratic or Authoritarian National Surveillance State with respect to
the natural law treatment of human civil liberties?
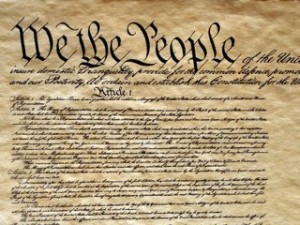
Since 1994 Internet access and utilization has increased globally at an exponential rate. With the recent revelations of U.S. Government intelligence agencies ongoing procedural extraction of personal and private data under the Foreign Intelligence Services Act (FISA) and National Security Letters (NSL) from large U.S. based technology companies.(1) This research blog hypothesizes that such an expansive collection, warehousing, and analyzing of data by the U.S. Government negatively impacts the Constitutional rights of U.S. citizens, natural rights of foreigners, is immoral, and in violation of the fourth amendment of the United States Constitution.
Analysis will begin with looking at the U.S. Government surveillance practices through Jack Balkin’s framework for understanding the constitutionality of the national surveillance state.(2) In addition the analysis will extend to illuminate how a national surveillance state and its fundamental nature encroaches and even breaches our rights and freedoms.(3)
After examining the U.S. as a National Surveillance state it is meaningful to understand the legal structure and nature of the U.S. national surveillance state and how it has changed over time.(4) This section will explore the development of the Foreign Intelligence Surveillance Act and the meaningful utilization of National Security Letters in the context of collecting and storing individual data sets on people, both foreign and domestic.(5) Lastly, this section will close with discussion surrounding the interpretation of the fourth amendment of the U.S. Constitution and the genesis of its origination through examining the historical use and tenets argued against “Writs of Assistance” by James Otis in 1761.(6) It was James Otis’s contention that blanket warrants were in violation of the British unwritten constitution going back to the Magna Carta created in 1215.(7) It was argued, that any law in violation of the Constitution or “natural law” that it was based on, was null and void.(8)
The final section will compose arguments based on the aforementioned analysis. This dialog will discuss the morality of the existence of a large and dynamic digital database on every human being that is being utilized by the most powerful government in the world under the guise of National Security against terrorism. The exploration will also discuss the question of whether Terrorism in of itself is a necessary or merely a sufficient condition for the basis of such a large and dynamic database to exist.
In light of how the recent national security information leaks occurred and exposed the existence of this database.(9) How those data breaches manifested is critically important to the morality argument in part and in whole. The mere existence of this database opens the distinct possibility of current and future generations of governance administrations to opportunistically change its meaningful utilization. In addition, given information on this intelligence program was stolen and publicly exposed, opens the question of the U.S. Governments’ basic ability to sufficiently protect this powerful and digital national surveillance apparatus from theft and future illicit use from that theft.
Specific Aims:
The nature of the U.S. National Surveillance State is in question
- Is the U.S. a democratic or authoritarian national surveillance state?
- What threats does the National Surveillance State pose to our freedoms?
- How do these threats manifest themselves?
The legal nature of the U.S. National Surveillance State is in question
- What is the meaningful use of FISA Courts and National Security Letters?
- How is the U.S. Constitution’s 4th amendment currently interpreted?
- What is a “writ of assistance” and does it apply in today’s context?
The morality of blanket data surveillance on foreign and U.S. domestic people needs examination
- Is terrorism a necessary or sufficient condition to blanket data collection?
- Is having one central database on all of humanity immoral?
- What is the probability this system is sufficiently secure from theft and illicit use?
Coming up Next: Background
Pingback: Thoughts – The Tools of Argument | @The Heart of Big Brother
Pingback: Thougths – What does Obama & His NSA Review Panel really think about security & Surveillance? | @The Heart of Big Brother
Pingback: Thoughts – What do America’s top liberal legal scholars think about surveillance, governance, and their own ideas? | @The Heart of Big Brother
Pingback: Thoughts – A Reasonable Articulable Suspicion Regarding Conspiracy Theories and Government Surveillance of U.S. Citizens | @The Heart of Big Brother
Pingback: Thoughts – How can the U.S. Government restrict our First Amendment Rights? | @The Heart of Big Brother